Wireless Vulnerabilities Threaten Trade Secrets, Says Bastille Report

Bastille Networks has announced the release of its inaugural annual threat report, “The State of Wireless Security in 2026,” revealing a dramatic surge in wireless vulnerabilities that are reshaping enterprise risk in a world that is increasingly operating in a wireless environment.

Wi-Fi, Bluetooth, Zigbee, LTE, and 5G networks have all become foundational to business and government operations around the world. Yet wireless vulnerabilities and exposures are accelerating at an unprecedented pace, with an average of 2.5 discovered per day in 2025 alone. Despite this environment, traditional vulnerability management models that rely on asset inventories, patch tracking, and IP-based scanning fail to address wireless risks and exposure.
“We’ve long said that wireless threats are proliferating, and this report illustrates the alarming extent to which that is the case as well as highlights the theft and espionage risks companies and governments face,” said Bastille CEO Chris Risley. “Anything that can be controlled wirelessly is vulnerable. With the explosion of new AI data centers and other high-value targets worth billions of dollars in intellectual property or trade secrets, now is the time for enterprises to start treating wireless visibility and vulnerability management as foundational security infrastructure.”
Key Findings from the 2026 Report:
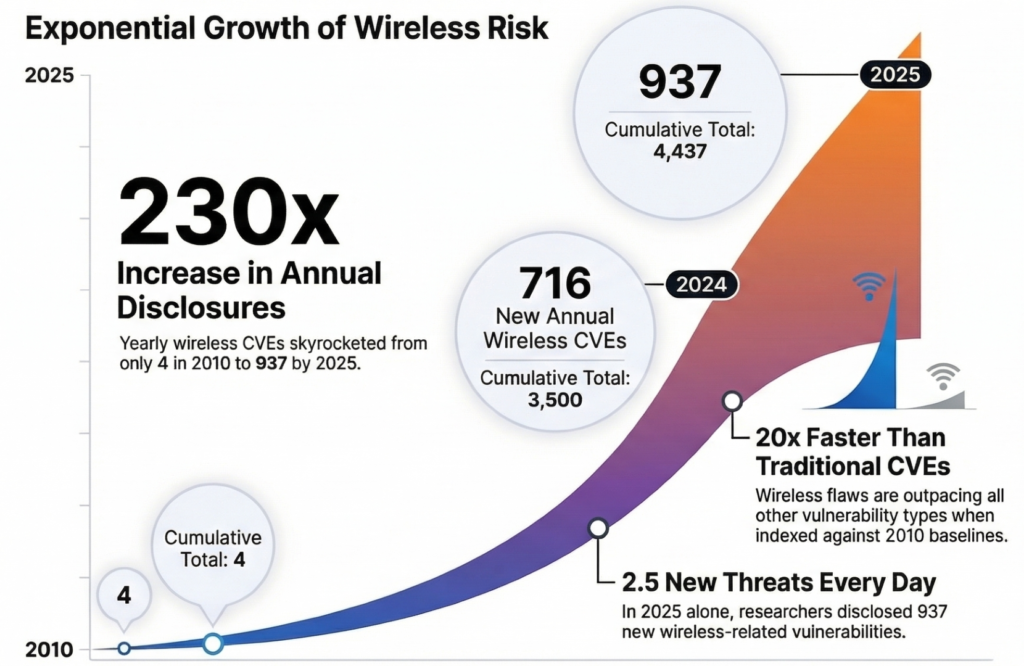
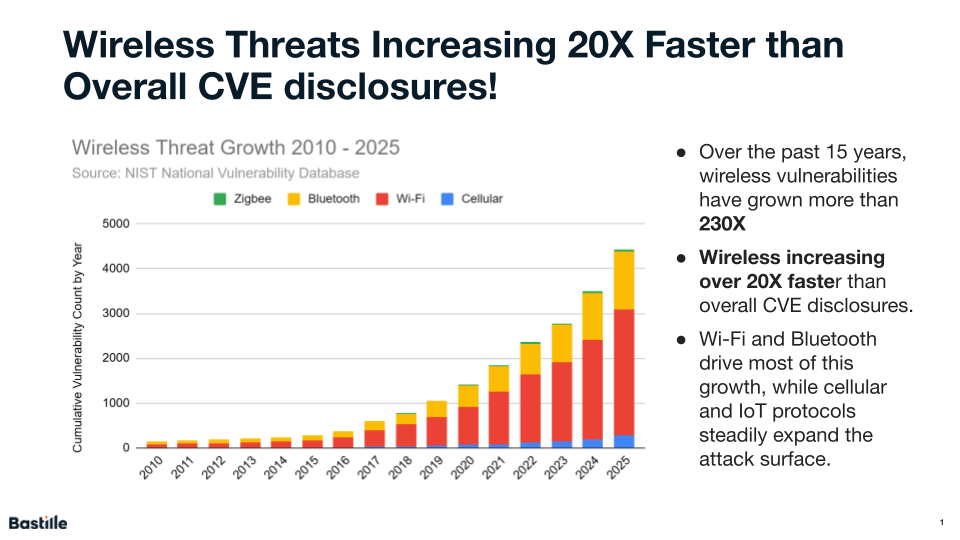
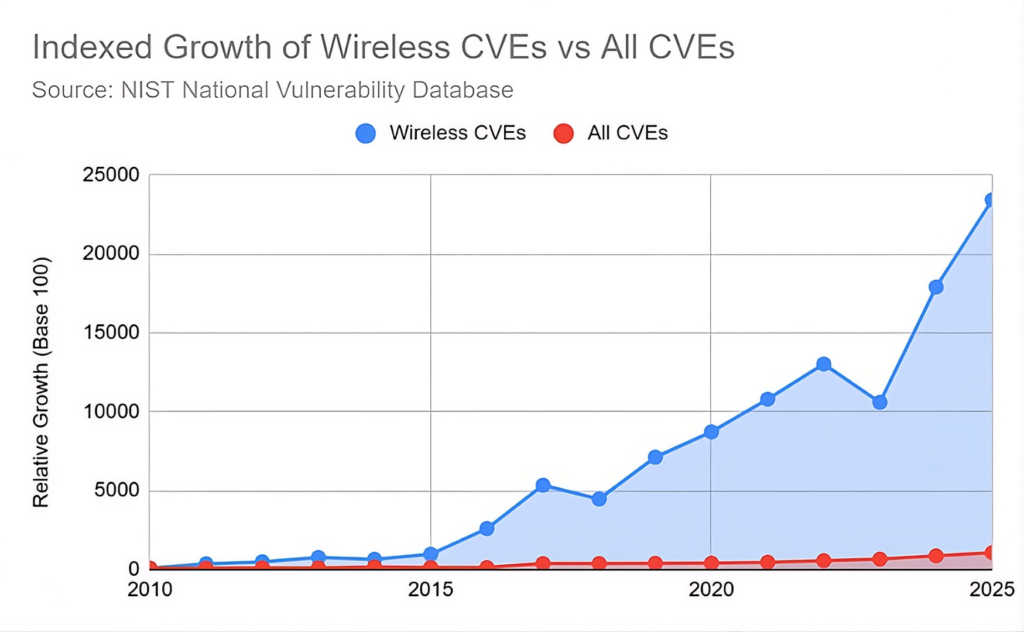
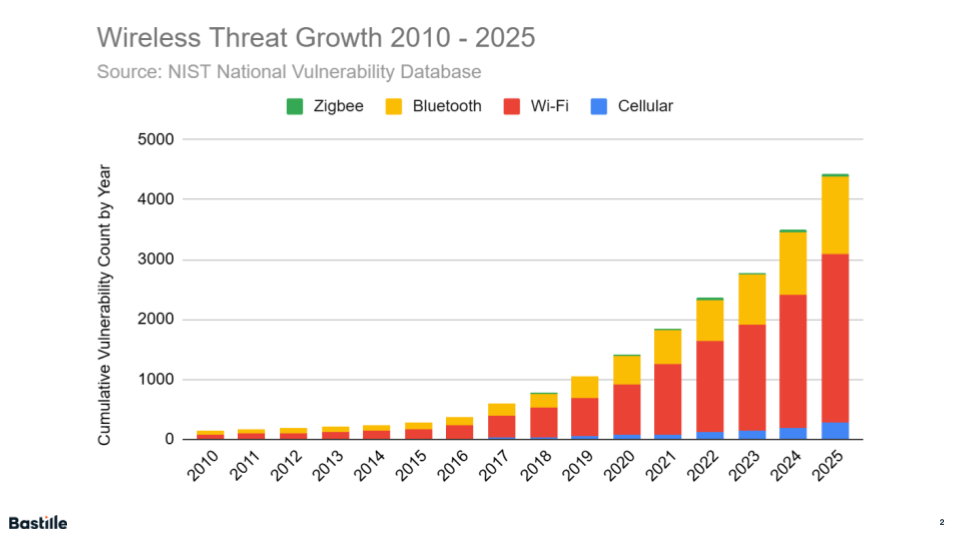
- Exponential Growth: Annual wireless vulnerabilities have grown by more than 230x over the last 15 years, jumping from just four reported Common Vulnerabilities Exposures (CVEs) in 2010 to 937 in 2025, with cumulative totals consistently doubling every 2-4 years over the last 12 years.
- Sustained Acceleration: The industry has seen two consecutive years of cumulative growth exceeding 25% (2024 and 2025), with a combined 60% increase in wireless vulnerabilities since the start of 2024.
- Daily Threat Velocity: In 2025 alone, researchers disclosed 937 new wireless CVEs, averaging 2.5 new vulnerabilities discovered every day.
- Protocol Dominance: Wi-Fi remains the largest source of disclosed vulnerabilities, accounting for over 60% of wireless CVEs, followed by Bluetooth, cellular, and Zigbee.
“What we’re seeing in the data is not a short-term spike but a structural shift in the threat landscape,” said Dr. Brett Walkenhorst, principal researcher and CTO at Bastille Networks. “Wireless vulnerabilities have grown more than 230-fold since 2010 and are accelerating far faster than the overall CVE ecosystem. Because many of these vulnerabilities affect shared chipsets, protocol stacks, and embedded systems that remain in service for years, each year’s disclosures compound a growing base of persistent exposure for enterprises.”
Wireless vulnerabilities will undoubtedly continue to rise in 2026 and beyond as wireless technologies expand into a broader range of enterprise and critical infrastructure use cases and as nation-state actors are likely to play an increasing role in wireless attacks, according to the report. Organizations are increasingly relying on wireless connectivity not only for workforce mobility, but also for building automation, industrial sensors, access control, logistics tracking, and embedded medical and manufacturing devices.
Bastille has been supporting the Intelligence Community and major corporations around the world for years by safeguarding classified information and trade secrets, and by deploying its technology that scans the airspace in key environments such as SCIFs, R&D facilities, data centers, and corporate headquarters. The always-on support helps to detect, classify, and locate every wireless transmitter in a facility – from authorized infrastructure to unmanaged personal peripherals and rogue devices.
Wireless airspace visibility enables security teams to identify threats that bypass traditional perimeters, such as data exfiltration via bugs with cellular modems or unauthorized Bluetooth connections. As the report shows, nation-state actors and foreign government-backed criminal organizations are finding new and increasingly sophisticated ways to exploit wireless vulnerabilities.
The report also notes that wireless vulnerabilities often persist in areas where traditional security controls provide limited visibility, including firmware, drivers, chipsets, and embedded stacks. These weaknesses can be exploited without IP connectivity and often impact multiple vendors due to shared components, making patching inconsistent or impossible for many devices.
To mitigate these risks, Bastille recommends that organizations move beyond traditional vulnerability management and adopt continuous, passive RF spectrum monitoring. By observing the airspace directly, security teams can detect anomalous behavior, such as unauthorized Bluetooth pairing attempts or rogue wireless access points, providing a layer of defense that traditional scanners and endpoint tools cannot see.




