
As global parcel volume surpasses 161 billion annually, cybercriminals are increasingly exploiting the “modern-day essential service” of courier delivery. New research into the Middle East and Africa (MEA) region from Group-IB reveals a growth in Fake Shipment Tracking Scams throughout 2025 and early 2026, driven by sophisticated Phishing-as-a-Service (PhaaS) platforms.
Researchers have identified a coordinated campaign using Sender ID Spoofing and real-time keylogging to steal personal information, banking credentials, and OTPs from unsuspecting residents waiting for deliveries.
The Anatomy of the Scam
The scheme leverages “delivery anxiety” at scale. It typically begins with an anonymous SMS claiming a delivery has failed or a package has been returned. Victims are urged to “update address information” or pay “handling fees” via a link.
Behind the link is a sophisticated phishing page designed to look official. Technical analysis reveals:
- Real-Time Exfiltration: The use of WebSockets allows attackers to log keystrokes (card numbers, CVV, OTPs) in real-time as the victim types them.
- Infrastructure Overlap: Many sites share infrastructure associated with Darcula, a PhaaS platform offering over 20,000 counterfeit domains and 200 phishing templates.
- Sender ID Spoofing: Attackers use illegal SMS gateways to merge fraudulent messages into legitimate message threads from trusted postal services, making them nearly indistinguishable from genuine communications.
Regional Impact
While the scheme is prevalent and targets multiple countries around the world, the MEA region has seen significant activity between December 2025 and February 2026. Top affected countries include Egypt and South Africa.
The fake shipment tracking scam primarily exploits the widespread reliance on parcel delivery services, making it one of the most prevalent phishing schemes observed by Group-IB researchers. As online shopping and logistics services are deeply embedded in everyday activities, a broad segment of the population is exposed to this threat.
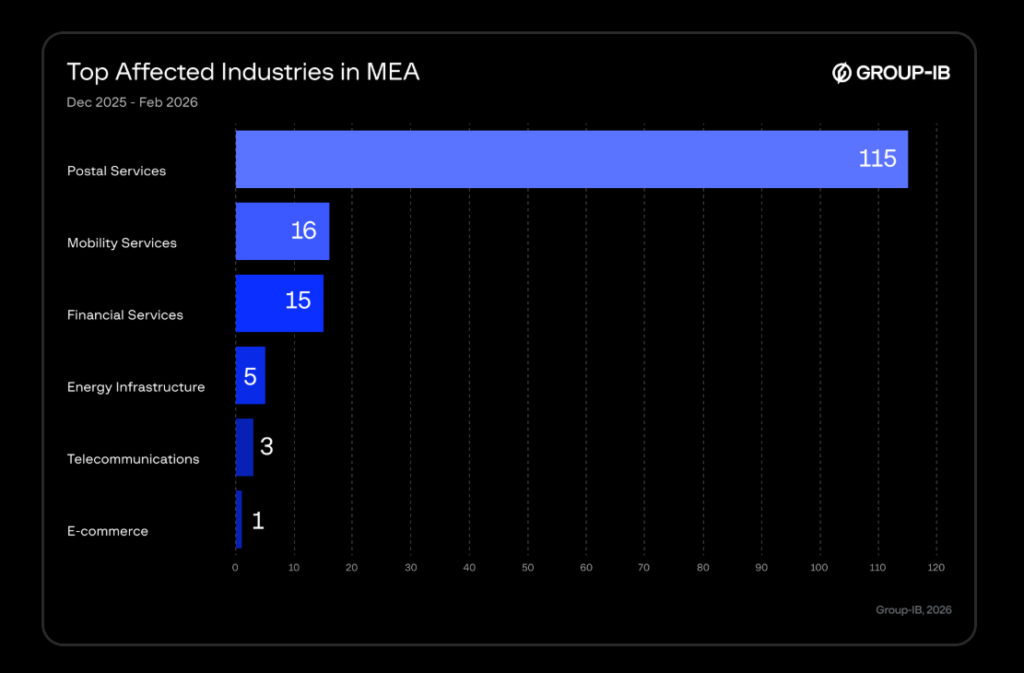
However, analysis indicates that certain sectors are disproportionately targeted, with postal and delivery services representing the most frequently abused category, followed by financial services, telecommunications, mobility services, and e-commerce platforms in the MEA region.
Expert Recommendations for Protection
As these fraudulent messages continue to circulate globally, understanding how they work is the first step in protection. The following defensive measures are recommended:
For Individuals:
- Verify Manually: Never click on tracking links sent via SMS or WhatsApp. Instead, manually visit the courier’s official website and enter your tracking number.
- Check the Sender: Real delivery companies do not use random mobile numbers or private email addresses.
- Be Suspicious of Urgency: Phishing relies on high-pressure tactics to bypass common sense. If a message demands immediate payment for an “address update,” it is likely a scam.
- Look for Domain Red Flags: Scammers favor low-cost, disposable extensions such as .xyz, .sbs, .top, and .click.
- Report Suspicious Activity: Forward scam messages to your local postal service or cybersecurity authority to help protect others.
For Businesses and Platforms:
- Public Education: Regularly publish alerts about ongoing phishing attempts using your brand.
- Domain Security: Implement protocols like DMARC, SPF, and DKIM to reduce the likelihood of emails being sent under your company name.
- Verification Tools: Provide a public tool on your official website where customers can verify tracking numbers and official communication channels.
- Proactive Monitoring: Utilize Digital Risk Protection services to track and take down fraudulent pages and domains impersonating your brand.




