News
-

Kaspersky Expands its Product Portfolio for Security Researchers
Kaspersky sandboxing technology is now available for use in customer networks. The on-premises Kaspersky Research Sandbox is designed for organizations…
Read More » -

Frost & Sullivan Presents Top Sensor Technologies Impacting the Future of Smart Cities
Frost & Sullivan’s recent analysis, Opportunities of Emerging Sensor Technologies Impacting the Future of Smart Cities, reports that digitization and…
Read More » -

ASUS Launches the ExpertBook B9
ASUS Middle East has announced the ExpertBook B9 laptop (B9450), thus launching the new ASUS ExpertBook series in the UAE…
Read More » -
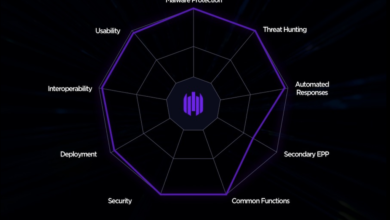
SentinelOne Receives Strong Ratings in Security and Interoperability From KuppingerCole
SentinelOne has been recognised as the Endpoint Protection, Detection, and Response (EPDR) featured innovation vendor in KuppingerCole’s 2020 Market Compass…
Read More » -

NetApp Updates its Unified Partner Program
NetApp has updated its Unified Partner Program to complement and align with its partners’ business capabilities and models. NetApp’s award-winning…
Read More » -

Avaya’s Partner Airtel to Enable Remote Work and Learning in Nigeria
Leading telecommunications services provider, Airtel Nigeria, has partnered with Avaya Holdings Corp., to enable organizations in the country to implement…
Read More » -

Aruba Launches Instant On AP22 Access Point
Aruba has launched its first Instant On Wi-Fi 6 access point: AP22. According to the company, the device offers higher…
Read More » -

Help AG Partners with CrowdStrike
With the protection of endpoint devices being a prime concern for businesses as they adapt to increased remote working in…
Read More » -

Ransomware Attack at Canon? 10TB Data Allegedly Stolen
Multinational corporation Canon reportedly fell victim to a ransomware attack launched by Maze group against its email and storage services…
Read More » -

Video: Qualys Brings a New Multi-Vector Approach of its Highly Scalable Cloud Platform to EDR
Traditional EDR Solutions focus only on end point activity to detect attacks. As a result, they lack the full context…
Read More »
